Противодействие хакерским угрозам
Модераторы: Olej, adminn, vikos
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 01 янв 2017, 21:34
Кто-то наследил…
Кто-то особенно умный смог обойти наш брандмауэр, пройти мимо Snort, получить права root в системе и теперь ходит в систему регулярно, используя установленный бэкдор. Нехорошо, бэкдор надо найти, удалить, а систему обновить. Для поиска руткитов и бэкдоров используем rkhunter:
Запускаем:
Софтина проверит всю систему на наличие руткитов и выведет на экран результаты. Если зловред все-таки найдется, rkhunter укажет на место и его можно будет затереть.
Код: Выделить всё
[olej@dell ~]$ dnf list rkhunter
Последняя проверка окончания срока действия метаданных: 1 day, 3:59:49 назад, Sat Dec 31 16:28:58 2016.
Доступные пакеты
rkhunter.noarch 1.4.2-11.fc23 updates
[olej@dell ~]$ sudo dnf install rkhunter
[sudo] пароль для olej:
Последняя проверка окончания срока действия метаданных: 0:22:25 назад, Sun Jan 1 20:11:17 2017.
Зависимости разрешены.
=======================================================================================================================================
Package Архитектура Версия Репозиторий Размер
=======================================================================================================================================
Установка:
rkhunter noarch 1.4.2-11.fc23 updates 201 k
Результат операции
=======================================================================================================================================
Установка 1 Пакет
Объем загрузки: 201 k
Объем изменений: 794 k
Продолжить? [д/Н]: y
Загрузка пакетов:
rkhunter-1.4.2-11.fc23.noarch.rpm 838 kB/s | 201 kB 00:00
---------------------------------------------------------------------------------------------------------------------------------------
Общий размер 124 kB/s | 201 kB 00:01
Проверка транзакции
Проверка транзакции успешно завершена.
Идет проверка транзакции
Тест транзакции проведен успешно
Выполнение транзакции
Установка : rkhunter-1.4.2-11.fc23.noarch 1/1
Проверка : rkhunter-1.4.2-11.fc23.noarch 1/1
Установлено:
rkhunter.noarch 1.4.2-11.fc23
Выполнено!
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 01 янв 2017, 21:40
Olej писал(а):
Для поиска руткитов и бэкдоров используем rkhunter:
Код: Выделить всё
[olej@dell ~]$ time sudo rkhunter -c --sk
[ Rootkit Hunter version 1.4.2 ]
Checking system commands...
Performing 'strings' command checks
Checking 'strings' command [ OK ]
Performing 'shared libraries' checks
Checking for preloading variables [ None found ]
Checking for preloaded libraries [ None found ]
Checking LD_LIBRARY_PATH variable [ Not found ]
Performing file properties checks
Checking for prerequisites [ Warning ]
/usr/sbin/adduser [ OK ]
/usr/sbin/chkconfig [ OK ]
/usr/sbin/chroot [ OK ]
/usr/sbin/depmod [ OK ]
/usr/sbin/fsck [ OK ]
/usr/sbin/fuser [ OK ]
/usr/sbin/groupadd [ OK ]
/usr/sbin/groupdel [ OK ]
/usr/sbin/groupmod [ OK ]
/usr/sbin/grpck [ OK ]
/usr/sbin/ifconfig [ OK ]
/usr/sbin/ifdown [ Warning ]
/usr/sbin/ifup [ Warning ]
/usr/sbin/init [ OK ]
/usr/sbin/insmod [ OK ]
/usr/sbin/ip [ OK ]
/usr/sbin/lsmod [ OK ]
/usr/sbin/lsof [ OK ]
/usr/sbin/modinfo [ OK ]
/usr/sbin/modprobe [ OK ]
/usr/sbin/nologin [ OK ]
/usr/sbin/pwck [ OK ]
/usr/sbin/rmmod [ OK ]
/usr/sbin/route [ OK ]
/usr/sbin/rsyslogd [ OK ]
/usr/sbin/runlevel [ OK ]
/usr/sbin/sestatus [ OK ]
/usr/sbin/sshd [ OK ]
/usr/sbin/sulogin [ OK ]
/usr/sbin/sysctl [ OK ]
/usr/sbin/tcpd [ OK ]
/usr/sbin/useradd [ OK ]
/usr/sbin/userdel [ OK ]
/usr/sbin/usermod [ OK ]
/usr/sbin/vipw [ OK ]
/usr/bin/awk [ OK ]
/usr/bin/basename [ OK ]
/usr/bin/bash [ OK ]
/usr/bin/cat [ OK ]
/usr/bin/chattr [ OK ]
/usr/bin/chmod [ OK ]
/usr/bin/chown [ OK ]
/usr/bin/cp [ OK ]
/usr/bin/curl [ OK ]
/usr/bin/cut [ OK ]
/usr/bin/date [ OK ]
/usr/bin/df [ OK ]
/usr/bin/diff [ OK ]
/usr/bin/dirname [ OK ]
/usr/bin/dmesg [ OK ]
/usr/bin/du [ OK ]
/usr/bin/echo [ OK ]
/usr/bin/ed [ OK ]
/usr/bin/egrep [ Warning ]
/usr/bin/env [ OK ]
/usr/bin/fgrep [ Warning ]
/usr/bin/file [ OK ]
/usr/bin/find [ OK ]
/usr/bin/GET [ OK ]
/usr/bin/grep [ OK ]
/usr/bin/groups [ OK ]
/usr/bin/head [ OK ]
/usr/bin/id [ OK ]
/usr/bin/kill [ OK ]
/usr/bin/killall [ OK ]
/usr/bin/last [ OK ]
/usr/bin/lastlog [ OK ]
/usr/bin/ldd [ OK ]
/usr/bin/less [ OK ]
/usr/bin/locate [ OK ]
/usr/bin/logger [ OK ]
/usr/bin/login [ OK ]
/usr/bin/ls [ OK ]
/usr/bin/lsattr [ OK ]
/usr/bin/mail [ OK ]
/usr/bin/md5sum [ OK ]
/usr/bin/mktemp [ OK ]
/usr/bin/more [ OK ]
/usr/bin/mount [ OK ]
/usr/bin/mv [ OK ]
/usr/bin/netstat [ OK ]
/usr/bin/newgrp [ OK ]
/usr/bin/passwd [ OK ]
/usr/bin/perl [ OK ]
/usr/bin/pgrep [ OK ]
/usr/bin/ping [ OK ]
/usr/bin/pkill [ OK ]
/usr/bin/ps [ OK ]
/usr/bin/pstree [ OK ]
/usr/bin/pwd [ OK ]
/usr/bin/readlink [ OK ]
/usr/bin/rkhunter [ OK ]
/usr/bin/rpm [ OK ]
/usr/bin/runcon [ OK ]
/usr/bin/sed [ OK ]
/usr/bin/sh [ OK ]
/usr/bin/sha1sum [ OK ]
/usr/bin/sha224sum [ OK ]
/usr/bin/sha256sum [ OK ]
/usr/bin/sha384sum [ OK ]
/usr/bin/sha512sum [ OK ]
/usr/bin/size [ OK ]
/usr/bin/sort [ OK ]
/usr/bin/ssh [ OK ]
/usr/bin/stat [ OK ]
/usr/bin/strings [ OK ]
/usr/bin/su [ OK ]
/usr/bin/sudo [ OK ]
/usr/bin/tail [ OK ]
/usr/bin/telnet [ OK ]
/usr/bin/test [ OK ]
/usr/bin/top [ OK ]
/usr/bin/touch [ OK ]
/usr/bin/tr [ OK ]
/usr/bin/uname [ OK ]
/usr/bin/uniq [ OK ]
/usr/bin/users [ OK ]
/usr/bin/vmstat [ OK ]
/usr/bin/w [ OK ]
/usr/bin/watch [ OK ]
/usr/bin/wc [ OK ]
/usr/bin/wget [ OK ]
/usr/bin/whatis [ OK ]
/usr/bin/whereis [ OK ]
/usr/bin/which [ OK ]
/usr/bin/who [ OK ]
/usr/bin/whoami [ OK ]
/usr/bin/kmod [ OK ]
/usr/bin/systemctl [ OK ]
/usr/bin/gawk [ OK ]
/usr/bin/mailx [ OK ]
/usr/lib/systemd/systemd [ OK ]
Checking for rootkits...
Performing check of known rootkit files and directories
55808 Trojan - Variant A [ Not found ]
ADM Worm [ Not found ]
AjaKit Rootkit [ Not found ]
Adore Rootkit [ Not found ]
aPa Kit [ Not found ]
Apache Worm [ Not found ]
Ambient (ark) Rootkit [ Not found ]
Balaur Rootkit [ Not found ]
BeastKit Rootkit [ Not found ]
beX2 Rootkit [ Not found ]
BOBKit Rootkit [ Not found ]
cb Rootkit [ Not found ]
CiNIK Worm (Slapper.B variant) [ Not found ]
Danny-Boy's Abuse Kit [ Not found ]
Devil RootKit [ Not found ]
Dica-Kit Rootkit [ Not found ]
Dreams Rootkit [ Not found ]
Duarawkz Rootkit [ Not found ]
Enye LKM [ Not found ]
Flea Linux Rootkit [ Not found ]
Fu Rootkit [ Not found ]
Fuck`it Rootkit [ Not found ]
GasKit Rootkit [ Not found ]
Heroin LKM [ Not found ]
HjC Kit [ Not found ]
ignoKit Rootkit [ Not found ]
IntoXonia-NG Rootkit [ Not found ]
Irix Rootkit [ Not found ]
Jynx Rootkit [ Not found ]
KBeast Rootkit [ Not found ]
Kitko Rootkit [ Not found ]
Knark Rootkit [ Not found ]
ld-linuxv.so Rootkit [ Not found ]
Li0n Worm [ Not found ]
Lockit / LJK2 Rootkit [ Not found ]
Mood-NT Rootkit [ Not found ]
MRK Rootkit [ Not found ]
Ni0 Rootkit [ Not found ]
Ohhara Rootkit [ Not found ]
Optic Kit (Tux) Worm [ Not found ]
Oz Rootkit [ Not found ]
Phalanx Rootkit [ Not found ]
Phalanx2 Rootkit [ Not found ]
Phalanx2 Rootkit (extended tests) [ Not found ]
Portacelo Rootkit [ Not found ]
R3dstorm Toolkit [ Not found ]
RH-Sharpe's Rootkit [ Not found ]
RSHA's Rootkit [ Not found ]
Scalper Worm [ Not found ]
Sebek LKM [ Not found ]
Shutdown Rootkit [ Not found ]
SHV4 Rootkit [ Not found ]
SHV5 Rootkit [ Not found ]
Sin Rootkit [ Not found ]
Slapper Worm [ Not found ]
Sneakin Rootkit [ Not found ]
'Spanish' Rootkit [ Not found ]
Suckit Rootkit [ Not found ]
Superkit Rootkit [ Not found ]
TBD (Telnet BackDoor) [ Not found ]
TeLeKiT Rootkit [ Not found ]
T0rn Rootkit [ Not found ]
trNkit Rootkit [ Not found ]
Trojanit Kit [ Not found ]
Tuxtendo Rootkit [ Not found ]
URK Rootkit [ Not found ]
Vampire Rootkit [ Not found ]
VcKit Rootkit [ Not found ]
Volc Rootkit [ Not found ]
Xzibit Rootkit [ Not found ]
zaRwT.KiT Rootkit [ Not found ]
ZK Rootkit [ Not found ]
Performing additional rootkit checks
Suckit Rookit additional checks [ OK ]
Checking for possible rootkit files and directories [ None found ]
Checking for possible rootkit strings [ None found ]
Performing malware checks
Checking running processes for suspicious files [ None found ]
Checking for hidden processes [ Skipped ]
Checking for login backdoors [ None found ]
Checking for suspicious directories [ None found ]
Checking for sniffer log files [ None found ]
Suspicious Shared Memory segments [ None found ]
Checking for Apache backdoor [ Not found ]
Performing Linux specific checks
Checking loaded kernel modules [ OK ]
Checking kernel module names [ OK ]
Checking the network...
Performing checks on the network ports
Checking for backdoor ports [ None found ]
Performing checks on the network interfaces
Checking for promiscuous interfaces [ None found ]
Checking the local host...
Performing system boot checks
Checking for local host name [ Found ]
Checking for system startup files [ Found ]
Checking system startup files for malware [ None found ]
Performing group and account checks
Checking for passwd file [ Found ]
Checking for root equivalent (UID 0) accounts [ None found ]
Checking for passwordless accounts [ None found ]
Checking for passwd file changes [ Warning ]
Checking for group file changes [ Warning ]
Checking root account shell history files [ OK ]
Performing system configuration file checks
Checking for an SSH configuration file [ Found ]
Checking if SSH root access is allowed [ Allowed ]
Checking if SSH protocol v1 is allowed [ Not set ]
Checking for a running system logging daemon [ Found ]
Checking for a system logging configuration file [ Found ]
Checking if syslog remote logging is allowed [ Not allowed ]
Performing filesystem checks
Checking /dev for suspicious file types [ None found ]
Checking for hidden files and directories [ None found ]
System checks summary
=====================
File properties checks...
Required commands check failed
Files checked: 132
Suspect files: 4
Rootkit checks...
Rootkits checked : 384
Possible rootkits: 0
Applications checks...
All checks skipped
The system checks took: 1 minute and 34 seconds
All results have been written to the log file: /var/log/rkhunter/rkhunter.log
One or more warnings have been found while checking the system.
Please check the log file (/var/log/rkhunter/rkhunter.log)
real 1m38.211s
user 0m37.310s
sys 1m23.876s
Обратите внимание на время выполнения.
Лог здесь:
Код: Выделить всё
[root@dell rkhunter]# tail /var/log/rkhunter/rkhunter.log
[20:37:22] Rootkit checks...
[20:37:22] Rootkits checked : 384
[20:37:22] Possible rootkits: 0
[20:37:22]
[20:37:22] Applications checks...
[20:37:22] All checks skipped
[20:37:22]
[20:37:22] The system checks took: 1 minute and 34 seconds
[20:37:22]
[20:37:22] Info: End date is Вс янв 1 20:37:22 EET 2017
Обновление базы данных руткитов:
Код: Выделить всё
[olej@dell ~]$ time sudo rkhunter --update
[sudo] пароль для olej:
[ Rootkit Hunter version 1.4.2 ]
Checking rkhunter data files...
Checking file mirrors.dat [ Updated ]
Checking file programs_bad.dat [ Updated ]
Checking file backdoorports.dat [ No update ]
Checking file suspscan.dat [ Updated ]
Checking file i18n/cn [ No update ]
Checking file i18n/de [ Updated ]
Checking file i18n/en [ No update ]
Checking file i18n/tr [ Updated ]
Checking file i18n/tr.utf8 [ Updated ]
Checking file i18n/zh [ Updated ]
Checking file i18n/zh.utf8 [ Updated ]
real 0m10.559s
user 0m1.558s
sys 0m2.916s
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 09 сен 2023, 19:09
Olej писал(а): ↑01 янв 2017, 21:34
Софтина проверит всю систему на наличие руткитов и выведет на экран результаты. Если зловред все-таки найдется, rkhunter укажет на место и его можно будет затереть.
Время прошло (6 лет) ... и система совсем другая...
Код: Выделить всё
olej@R420:~/2023/EmerCoin$ cat /etc/issue.net
Linux Mint 21.2 Victoria
Код: Выделить всё
olej@R420:~$ aptitude search rkhunter
p rkhunter - сканер руткитов, уязвимостей и эксплоитов
Код: Выделить всё
olej@R420:~$ sudo apt install rkhunter
[sudo] пароль для olej:
Чтение списков пакетов… Готово
Построение дерева зависимостей… Готово
Чтение информации о состоянии… Готово
Будут установлены следующие дополнительные пакеты:
libruby3.0 rake ruby ruby-net-telnet ruby-rubygems ruby-webrick ruby-xmlrpc ruby3.0 rubygems-integration unhide unhide.rb
Предлагаемые пакеты:
ri ruby-dev bundler
Следующие НОВЫЕ пакеты будут установлены:
libruby3.0 rake rkhunter ruby ruby-net-telnet ruby-rubygems ruby-webrick ruby-xmlrpc ruby3.0 rubygems-integration unhide unhide.rb
Обновлено 0 пакетов, установлено 12 новых пакетов, для удаления отмечено 0 пакетов, и 0 пакетов не обновлено.
Необходимо скачать 5.829 kB архивов.
После данной операции объём занятого дискового пространства возрастёт на 26,3 MB.
Хотите продолжить? [Д/н] y
Пол:1 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 rkhunter all 1.4.6-10 [220 kB]
Пол:2 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 rubygems-integration all 1.18 [5.336 B]
Пол:3 http://ubuntu.mirrors.omnilance.com/ubuntu jammy-updates/main amd64 ruby3.0 amd64 3.0.2-7ubuntu2.4 [50,1 kB]
Пол:4 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 ruby-rubygems all 3.3.5-2 [228 kB]
Пол:5 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 ruby amd64 1:3.0~exp1 [5.100 B]
Пол:6 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 rake all 13.0.6-2 [61,7 kB]
Пол:7 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 ruby-net-telnet all 0.1.1-2 [12,6 kB]
Пол:8 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 ruby-webrick all 1.7.0-3 [51,8 kB]
Пол:9 http://ubuntu.mirrors.omnilance.com/ubuntu jammy-updates/main amd64 ruby-xmlrpc all 0.3.2-1ubuntu0.1 [24,9 kB]
Пол:10 http://ubuntu.mirrors.omnilance.com/ubuntu jammy-updates/main amd64 libruby3.0 amd64 3.0.2-7ubuntu2.4 [5.113 kB]
Пол:11 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 unhide amd64 20130526-4ubuntu1 [47,7 kB]
Пол:12 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 unhide.rb all 22-6 [8.942 B]
Получено 5.829 kB за 3с (2.310 kB/s)
Предварительная настройка пакетов …
Выбор ранее не выбранного пакета rkhunter.
(Чтение базы данных … на данный момент установлено 569527 файлов и каталогов.)
Подготовка к распаковке …/00-rkhunter_1.4.6-10_all.deb …
Распаковывается rkhunter (1.4.6-10) …
Выбор ранее не выбранного пакета rubygems-integration.
Подготовка к распаковке …/01-rubygems-integration_1.18_all.deb …
Распаковывается rubygems-integration (1.18) …
Выбор ранее не выбранного пакета ruby3.0.
Подготовка к распаковке …/02-ruby3.0_3.0.2-7ubuntu2.4_amd64.deb …
Распаковывается ruby3.0 (3.0.2-7ubuntu2.4) …
Выбор ранее не выбранного пакета ruby-rubygems.
Подготовка к распаковке …/03-ruby-rubygems_3.3.5-2_all.deb …
Распаковывается ruby-rubygems (3.3.5-2) …
Выбор ранее не выбранного пакета ruby.
Подготовка к распаковке …/04-ruby_1%3a3.0~exp1_amd64.deb …
Распаковывается ruby (1:3.0~exp1) …
Выбор ранее не выбранного пакета rake.
Подготовка к распаковке …/05-rake_13.0.6-2_all.deb …
Распаковывается rake (13.0.6-2) …
Выбор ранее не выбранного пакета ruby-net-telnet.
Подготовка к распаковке …/06-ruby-net-telnet_0.1.1-2_all.deb …
Распаковывается ruby-net-telnet (0.1.1-2) …
Выбор ранее не выбранного пакета ruby-webrick.
Подготовка к распаковке …/07-ruby-webrick_1.7.0-3_all.deb …
Распаковывается ruby-webrick (1.7.0-3) …
Выбор ранее не выбранного пакета ruby-xmlrpc.
Подготовка к распаковке …/08-ruby-xmlrpc_0.3.2-1ubuntu0.1_all.deb …
Распаковывается ruby-xmlrpc (0.3.2-1ubuntu0.1) …
Выбор ранее не выбранного пакета libruby3.0:amd64.
Подготовка к распаковке …/09-libruby3.0_3.0.2-7ubuntu2.4_amd64.deb …
Распаковывается libruby3.0:amd64 (3.0.2-7ubuntu2.4) …
Выбор ранее не выбранного пакета unhide.
Подготовка к распаковке …/10-unhide_20130526-4ubuntu1_amd64.deb …
Распаковывается unhide (20130526-4ubuntu1) …
Выбор ранее не выбранного пакета unhide.rb.
Подготовка к распаковке …/11-unhide.rb_22-6_all.deb …
Распаковывается unhide.rb (22-6) …
Настраивается пакет rubygems-integration (1.18) …
Настраивается пакет unhide (20130526-4ubuntu1) …
Настраивается пакет ruby-net-telnet (0.1.1-2) …
Настраивается пакет ruby-webrick (1.7.0-3) …
Настраивается пакет ruby-xmlrpc (0.3.2-1ubuntu0.1) …
Настраивается пакет rkhunter (1.4.6-10) …
Creating config file /etc/default/rkhunter with new version
[ Rootkit Hunter version 1.4.6 ]
File created: searched for 183 files, found 157
Настраивается пакет rake (13.0.6-2) …
Настраивается пакет libruby3.0:amd64 (3.0.2-7ubuntu2.4) …
Настраивается пакет ruby-rubygems (3.3.5-2) …
Настраивается пакет ruby3.0 (3.0.2-7ubuntu2.4) …
Настраивается пакет ruby (1:3.0~exp1) …
Настраивается пакет unhide.rb (22-6) …
Обрабатываются триггеры для libc-bin (2.35-0ubuntu3.1) …
Обрабатываются триггеры для man-db (2.10.2-1) …
Обрабатываются триггеры для rkhunter (1.4.6-10) …
[ Rootkit Hunter version 1.4.6 ]
File updated: searched for 183 files, found 157
Код: Выделить всё
root@R420:~# which rkhunter
/usr/bin/rkhunter
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 09 сен 2023, 19:25
Olej писал(а): ↑09 сен 2023, 19:09
система совсем другая...
Код: Выделить всё
root@R420:~# sudo rkhunter --help
Usage: rkhunter {--check | --unlock | --update | --versioncheck |
--propupd [{filename | directory | package name},...] |
--list [{tests | {lang | languages} | rootkits | perl | propfiles}] |
--config-check | --version | --help} [options]
Current options are:
--append-log Append to the logfile, do not overwrite
--bindir <directory>... Use the specified command directories
-c, --check Check the local system
-C, --config-check Check the configuration file(s), then exit
--cs2, --color-set2 Use the second color set for output
--configfile <file> Use the specified configuration file
--cronjob Run as a cron job
(implies -c, --sk and --nocolors options)
--dbdir <directory> Use the specified database directory
--debug Debug mode
(Do not use unless asked to do so)
--disable <test>[,<test>...] Disable specific tests
(Default is to disable no tests)
--display-logfile Display the logfile at the end
--enable <test>[,<test>...] Enable specific tests
(Default is to enable all tests)
--hash {MD5 | SHA1 | SHA224 | SHA256 | SHA384 | SHA512 |
NONE | <command>} Use the specified file hash function
(Default is SHA256)
-h, --help Display this help menu, then exit
--lang, --language <language> Specify the language to use
(Default is English)
--list [tests | languages | List the available test names, languages,
rootkits | perl | rootkit names, perl module status
propfiles] or file properties database, then exit
-l, --logfile [file] Write to a logfile
(Default is /var/log/rkhunter.log)
--noappend-log Do not append to the logfile, overwrite it
--nocf Do not use the configuration file entries
for disabled tests (only valid with --disable)
--nocolors Use black and white output
--nolog Do not write to a logfile
--nomow, --no-mail-on-warning Do not send a message if warnings occur
--ns, --nosummary Do not show the summary of check results
--novl, --no-verbose-logging No verbose logging
--pkgmgr {RPM | DPKG | BSD | Use the specified package manager to obtain
BSDng | SOLARIS | or verify file property values.
NONE} (Default is NONE)
--propupd [file | directory | Update the entire file properties database,
package]... or just for the specified entries
-q, --quiet Quiet mode (no output at all)
--rwo, --report-warnings-only Show only warning messages
--sk, --skip-keypress Don't wait for a keypress after each test
--summary Show the summary of system check results
(This is the default)
--syslog [facility.priority] Log the check start and finish times to syslog
(Default level is authpriv.notice)
--tmpdir <directory> Use the specified temporary directory
--unlock Unlock (remove) the lock file
--update Check for updates to database files
--vl, --verbose-logging Use verbose logging (on by default)
-V, --version Display the version number, then exit
--versioncheck Check for latest version of program
-x, --autox Automatically detect if X is in use
-X, --no-autox Do not automatically detect if X is in use
Код: Выделить всё
olej@R420:~$ time sudo rkhunter --check
[ Rootkit Hunter version 1.4.6 ]
Checking system commands...
Performing 'strings' command checks
Checking 'strings' command [ OK ]
Performing 'shared libraries' checks
Checking for preloading variables [ None found ]
Checking for preloaded libraries [ None found ]
Checking LD_LIBRARY_PATH variable [ Not found ]
Performing file properties checks
Checking for prerequisites [ OK ]
/usr/sbin/adduser [ OK ]
/usr/sbin/chroot [ OK ]
/usr/sbin/cron [ OK ]
/usr/sbin/depmod [ OK ]
/usr/sbin/fsck [ OK ]
/usr/sbin/groupadd [ OK ]
/usr/sbin/groupdel [ OK ]
/usr/sbin/groupmod [ OK ]
/usr/sbin/grpck [ OK ]
/usr/sbin/ifconfig [ OK ]
/usr/sbin/ifdown [ OK ]
/usr/sbin/ifup [ OK ]
/usr/sbin/inetd [ OK ]
/usr/sbin/init [ OK ]
/usr/sbin/insmod [ OK ]
/usr/sbin/ip [ OK ]
/usr/sbin/lsmod [ OK ]
/usr/sbin/modinfo [ OK ]
/usr/sbin/modprobe [ OK ]
/usr/sbin/nologin [ OK ]
/usr/sbin/pwck [ OK ]
/usr/sbin/rmmod [ OK ]
/usr/sbin/route [ OK ]
/usr/sbin/rsyslogd [ OK ]
/usr/sbin/runlevel [ OK ]
/usr/sbin/sshd [ OK ]
/usr/sbin/sulogin [ OK ]
/usr/sbin/sysctl [ OK ]
/usr/sbin/tcpd [ OK ]
/usr/sbin/useradd [ OK ]
/usr/sbin/userdel [ OK ]
/usr/sbin/usermod [ OK ]
/usr/sbin/vipw [ OK ]
/usr/sbin/unhide [ OK ]
/usr/sbin/unhide-linux [ OK ]
/usr/sbin/unhide-posix [ OK ]
/usr/sbin/unhide-tcp [ OK ]
/usr/bin/awk [ OK ]
/usr/bin/basename [ OK ]
/usr/bin/bash [ OK ]
/usr/bin/cat [ OK ]
/usr/bin/chattr [ OK ]
/usr/bin/chmod [ OK ]
/usr/bin/chown [ OK ]
/usr/bin/cp [ OK ]
/usr/bin/curl [ OK ]
/usr/bin/cut [ OK ]
/usr/bin/date [ OK ]
/usr/bin/df [ OK ]
/usr/bin/diff [ OK ]
/usr/bin/dirname [ OK ]
/usr/bin/dmesg [ OK ]
/usr/bin/dpkg [ OK ]
/usr/bin/dpkg-query [ OK ]
/usr/bin/du [ OK ]
/usr/bin/echo [ OK ]
/usr/bin/ed [ OK ]
/usr/bin/egrep [ OK ]
/usr/bin/env [ OK ]
/usr/bin/fgrep [ OK ]
/usr/bin/file [ OK ]
/usr/bin/find [ OK ]
/usr/bin/fuser [ OK ]
/usr/bin/GET [ OK ]
/usr/bin/grep [ OK ]
/usr/bin/groups [ OK ]
/usr/bin/head [ OK ]
/usr/bin/id [ OK ]
/usr/bin/ip [ OK ]
/usr/bin/ipcs [ OK ]
/usr/bin/kill [ OK ]
/usr/bin/killall [ OK ]
/usr/bin/last [ OK ]
/usr/bin/lastlog [ OK ]
/usr/bin/ldd [ OK ]
/usr/bin/less [ OK ]
/usr/bin/links [ OK ]
/usr/bin/locate [ OK ]
/usr/bin/logger [ OK ]
/usr/bin/login [ OK ]
/usr/bin/ls [ OK ]
/usr/bin/lsattr [ OK ]
/usr/bin/lsmod [ OK ]
/usr/bin/lsof [ OK ]
/usr/bin/lynx [ OK ]
/usr/bin/mail [ OK ]
/usr/bin/md5sum [ OK ]
/usr/bin/mktemp [ OK ]
/usr/bin/more [ OK ]
/usr/bin/mount [ OK ]
/usr/bin/mv [ OK ]
/usr/bin/netstat [ OK ]
/usr/bin/newgrp [ OK ]
/usr/bin/passwd [ OK ]
/usr/bin/perl [ OK ]
/usr/bin/pgrep [ OK ]
/usr/bin/ping [ OK ]
/usr/bin/pkill [ OK ]
/usr/bin/ps [ OK ]
/usr/bin/pstree [ OK ]
/usr/bin/pwd [ OK ]
/usr/bin/readlink [ OK ]
/usr/bin/rkhunter [ OK ]
/usr/bin/runcon [ OK ]
/usr/bin/sed [ OK ]
/usr/bin/sh [ OK ]
/usr/bin/sha1sum [ OK ]
/usr/bin/sha224sum [ OK ]
/usr/bin/sha256 [ OK ]
/usr/bin/sha256sum [ OK ]
/usr/bin/sha384 [ OK ]
/usr/bin/sha384sum [ OK ]
/usr/bin/sha512 [ OK ]
/usr/bin/sha512sum [ OK ]
/usr/bin/size [ OK ]
/usr/bin/sockstat [ OK ]
/usr/bin/sort [ OK ]
/usr/bin/ssh [ OK ]
/usr/bin/stat [ OK ]
/usr/bin/strace [ OK ]
/usr/bin/strings [ OK ]
/usr/bin/su [ OK ]
/usr/bin/sudo [ OK ]
/usr/bin/tail [ OK ]
/usr/bin/telnet [ OK ]
/usr/bin/test [ OK ]
/usr/bin/top [ OK ]
/usr/bin/touch [ OK ]
/usr/bin/tr [ OK ]
/usr/bin/uname [ OK ]
/usr/bin/uniq [ OK ]
/usr/bin/users [ OK ]
/usr/bin/vmstat [ OK ]
/usr/bin/w [ OK ]
/usr/bin/watch [ OK ]
/usr/bin/wc [ OK ]
/usr/bin/wget [ OK ]
/usr/bin/whatis [ OK ]
/usr/bin/whereis [ OK ]
/usr/bin/which [ OK ]
/usr/bin/who [ OK ]
/usr/bin/whoami [ OK ]
/usr/bin/numfmt [ OK ]
/usr/bin/kmod [ OK ]
/usr/bin/systemd [ OK ]
/usr/bin/systemctl [ OK ]
/usr/bin/gawk [ OK ]
/usr/bin/lwp-request [ Warning ]
/usr/bin/plocate [ OK ]
/usr/bin/mail.mailutils [ OK ]
/usr/bin/dash [ OK ]
/usr/bin/hashalot [ OK ]
/usr/bin/x86_64-linux-gnu-size [ OK ]
/usr/bin/x86_64-linux-gnu-strings [ OK ]
/usr/bin/telnet.netkit [ OK ]
/usr/bin/which.debianutils [ OK ]
/usr/lib/systemd/systemd [ OK ]
[Press <ENTER> to continue]
Checking for rootkits...
Performing check of known rootkit files and directories
55808 Trojan - Variant A [ Not found ]
ADM Worm [ Not found ]
AjaKit Rootkit [ Not found ]
Adore Rootkit [ Not found ]
aPa Kit [ Not found ]
Apache Worm [ Not found ]
Ambient (ark) Rootkit [ Not found ]
Balaur Rootkit [ Not found ]
BeastKit Rootkit [ Not found ]
beX2 Rootkit [ Not found ]
BOBKit Rootkit [ Not found ]
cb Rootkit [ Not found ]
CiNIK Worm (Slapper.B variant) [ Not found ]
Danny-Boy's Abuse Kit [ Not found ]
Devil RootKit [ Not found ]
Diamorphine LKM [ Not found ]
Dica-Kit Rootkit [ Not found ]
Dreams Rootkit [ Not found ]
Duarawkz Rootkit [ Not found ]
Ebury backdoor [ Not found ]
Enye LKM [ Not found ]
Flea Linux Rootkit [ Not found ]
Fu Rootkit [ Not found ]
Fuck`it Rootkit [ Not found ]
GasKit Rootkit [ Not found ]
Heroin LKM [ Not found ]
HjC Kit [ Not found ]
ignoKit Rootkit [ Not found ]
IntoXonia-NG Rootkit [ Not found ]
Irix Rootkit [ Not found ]
Jynx Rootkit [ Not found ]
Jynx2 Rootkit [ Not found ]
KBeast Rootkit [ Not found ]
Kitko Rootkit [ Not found ]
Knark Rootkit [ Not found ]
ld-linuxv.so Rootkit [ Not found ]
Li0n Worm [ Not found ]
Lockit / LJK2 Rootkit [ Not found ]
Mokes backdoor [ Not found ]
Mood-NT Rootkit [ Not found ]
MRK Rootkit [ Not found ]
Ni0 Rootkit [ Not found ]
Ohhara Rootkit [ Not found ]
Optic Kit (Tux) Worm [ Not found ]
Oz Rootkit [ Not found ]
Phalanx Rootkit [ Not found ]
Phalanx2 Rootkit [ Not found ]
Phalanx2 Rootkit (extended tests) [ Not found ]
Portacelo Rootkit [ Not found ]
R3dstorm Toolkit [ Not found ]
RH-Sharpe's Rootkit [ Not found ]
RSHA's Rootkit [ Not found ]
Scalper Worm [ Not found ]
Sebek LKM [ Not found ]
Shutdown Rootkit [ Not found ]
SHV4 Rootkit [ Not found ]
SHV5 Rootkit [ Not found ]
Sin Rootkit [ Not found ]
Slapper Worm [ Not found ]
Sneakin Rootkit [ Not found ]
'Spanish' Rootkit [ Not found ]
Suckit Rootkit [ Not found ]
Superkit Rootkit [ Not found ]
TBD (Telnet BackDoor) [ Not found ]
TeLeKiT Rootkit [ Not found ]
T0rn Rootkit [ Not found ]
trNkit Rootkit [ Not found ]
Trojanit Kit [ Not found ]
Tuxtendo Rootkit [ Not found ]
URK Rootkit [ Not found ]
Vampire Rootkit [ Not found ]
VcKit Rootkit [ Not found ]
Volc Rootkit [ Not found ]
Xzibit Rootkit [ Not found ]
zaRwT.KiT Rootkit [ Not found ]
ZK Rootkit [ Not found ]
[Press <ENTER> to continue]
Performing additional rootkit checks
Suckit Rootkit additional checks [ OK ]
Checking for possible rootkit files and directories [ None found ]
Checking for possible rootkit strings [ None found ]
Performing malware checks
Checking running processes for suspicious files [ None found ]
Checking for login backdoors [ None found ]
Checking for sniffer log files [ None found ]
Checking for suspicious directories [ None found ]
Checking for suspicious (large) shared memory segments [ Warning ]
Performing trojan specific checks
Checking for enabled inetd services [ OK ]
Checking for Apache backdoor [ Not found ]
Performing Linux specific checks
Checking loaded kernel modules [ OK ]
Checking kernel module names [ OK ]
[Press <ENTER> to continue]
Checking the network...
Performing checks on the network ports
Checking for backdoor ports [ None found ]
Performing checks on the network interfaces
Checking for promiscuous interfaces [ None found ]
Checking the local host...
Performing system boot checks
Checking for local host name [ Found ]
Checking for system startup files [ Found ]
Checking system startup files for malware [ None found ]
Performing group and account checks
Checking for passwd file [ Found ]
Checking for root equivalent (UID 0) accounts [ None found ]
Checking for passwordless accounts [ None found ]
Checking for passwd file changes [ None found ]
Checking for group file changes [ None found ]
Checking root account shell history files [ OK ]
Performing system configuration file checks
Checking for an SSH configuration file [ Found ]
Checking if SSH root access is allowed [ Warning ]
Checking if SSH protocol v1 is allowed [ Not set ]
Checking for other suspicious configuration settings [ None found ]
Checking for a running system logging daemon [ Found ]
Checking for a system logging configuration file [ Found ]
Checking if syslog remote logging is allowed [ Not allowed ]
Performing filesystem checks
Checking /dev for suspicious file types [ Warning ]
Checking for hidden files and directories [ Warning ]
[Press <ENTER> to continue]
System checks summary
=====================
File properties checks...
Files checked: 157
Suspect files: 1
Rootkit checks...
Rootkits checked : 504
Possible rootkits: 53
Applications checks...
All checks skipped
The system checks took: 6 minutes and 54 seconds
All results have been written to the log file: /var/log/rkhunter.log
One or more warnings have been found while checking the system.
Please check the log file (/var/log/rkhunter.log)
real 6m57,003s
user 0m0,019s
sys 0m0,026s
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 09 сен 2023, 19:35
Код: Выделить всё
...
All results have been written to the log file: /var/log/rkhunter.log
...
Код: Выделить всё
olej@R420:~$ ls -l /var/log/rkhunter.log
-rw------- 1 root root 137648 сен 9 19:22 /var/log/rkhunter.log
Ну ... как минимум, нужно разобраться:
Код: Выделить всё
root@R420:/var/log# grep Warning /var/log/rkhunter.log
[19:16:34] /usr/bin/lwp-request [ Warning ]
[19:16:34] Warning: The command '/usr/bin/lwp-request' has been replaced by a script: /usr/bin/lwp-request: Perl script text executable
[19:21:25] Checking for suspicious (large) shared memory segments [ Warning ]
[19:21:25] Warning: The following suspicious (large) shared memory segments have been found:
[19:22:43] Checking if SSH root access is allowed [ Warning ]
[19:22:43] Warning: The SSH configuration option 'PermitRootLogin' has not been set.
[19:22:48] Checking /dev for suspicious file types [ Warning ]
[19:22:48] Warning: Suspicious file types found in /dev:
[19:22:48] Checking for hidden files and directories [ Warning ]
[19:22:48] Warning: Hidden directory found: /etc/.java
[19:22:48] Warning: Hidden file found: /etc/.#dante.conf: broken symbolic link to root@R420.27288
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 22 сен 2023, 13:34
Поиск rootkit
apt-get install rkhunter — ставим прогу для поиска руткитов
rkhunter -c --sk — запуск поиска
rkhunter --update — апгрейд базы
apt-get install tiger — ставим еще одну прогу для поиска руткитов
tiger — запуск проверки
apt-get install lynis — ставим еще одну прогу для поиска руткитов
lynis -c — запуск проверки
Взломщики, которым успешно удалось проникнуть в систему, часто заменяют некоторые системные бинарные файлы (например, Is или ps) поврежденными версиями и делают их не отключаемыми. Поэтому полезно иногда проверять атрибуты, назначенные исполняемым файлам (например, в каталогах /bin, /usr/bin, /sbin и /usr/sbin).
Есть смысл поинтересоваться.
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 22 сен 2023, 13:49
Olej писал(а): ↑22 сен 2023, 13:34
Есть смысл поинтересоваться.
Всё под root! :
Код: Выделить всё
root@R420:~# rkhunter --update
Invalid WEB_CMD configuration option: Relative pathname: "/bin/false"
Облом-с

Код: Выделить всё
olej@R420:~/2023/own.BOOKs/NET$ grep -v ^# /etc/rkhunter.conf | grep -v ^$
UPDATE_MIRRORS=0
MIRRORS_MODE=1
TMPDIR=/var/lib/rkhunter/tmp
DBDIR=/var/lib/rkhunter/db
SCRIPTDIR=/usr/share/rkhunter/scripts
UPDATE_LANG="en"
LOGFILE=/var/log/rkhunter.log
USE_SYSLOG=authpriv.warning
AUTO_X_DETECT=1
ALLOW_SSH_PROT_V1=2
ENABLE_TESTS=ALL
DISABLE_TESTS=suspscan hidden_ports hidden_procs deleted_files packet_cap_apps apps
SCRIPTWHITELIST=/usr/bin/egrep
SCRIPTWHITELIST=/usr/bin/fgrep
SCRIPTWHITELIST=/usr/bin/which
SCRIPTWHITELIST=/usr/bin/ldd
SCRIPTWHITELIST=/usr/bin/which.debianutils
SCRIPTWHITELIST=/usr/sbin/adduser
WEB_CMD="/bin/false"
INSTALLDIR=/usr
Код: Выделить всё
olej@R420:~/2023/own.BOOKs/NET$ grep /bin/false /etc/rkhunter.conf -B20
#
# This allows the user to use a command other than the one automatically
# selected by rkhunter, but still one which it already knows about.
# For example:
#
# WEB_CMD=curl
#
# Alternatively, the user may specify a completely new command. However, note
# that rkhunter expects the downloaded file to be written to stdout, and that
# everything written to stderr is ignored. For example:
#
# WEB_CMD="/opt/bin/dlfile --timeout 5m -q"
#
# *BSD users may want to use the 'ftp' command, provided that it supports the
# HTTP protocol:
#
# WEB_CMD="ftp -o -"
#
# This option has no default value.
#
WEB_CMD="/bin/false"
Откуда оно взялось


Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 22 сен 2023, 13:55
Olej писал(а): ↑22 сен 2023, 13:49
Откуда оно взялось
Правлю:
Код: Выделить всё
olej@R420:~/2023/own.BOOKs/NET$ grep WEB_CMD= /etc/rkhunter.conf | grep -v ^#
WEB_CMD=curl
Код: Выделить всё
root@R420:~# time rkhunter --update
[ Rootkit Hunter version 1.4.6 ]
Checking rkhunter data files...
Checking file mirrors.dat [ Skipped ]
Checking file programs_bad.dat [ Update failed ]
Checking file backdoorports.dat [ Update failed ]
Checking file suspscan.dat [ Update failed ]
Checking file i18n versions [ Update failed ]
Please check the log file (/var/log/rkhunter.log)
real 0m2,048s
user 0m1,809s
sys 0m0,751s
Код: Выделить всё
root@R420:~# cat /var/log/rkhunter.log
[13:52:02] Running Rootkit Hunter version 1.4.6 on R420
[13:52:02]
[13:52:02] Info: Start date is Пт 22 сен 2023 13:52:02 EEST
[13:52:02]
[13:52:02] Checking configuration file and command-line options...
[13:52:02] Info: Detected operating system is 'Linux'
[13:52:02] Info: Found O/S name: Linux Mint 21.2
[13:52:02] Info: Command line is /usr/bin/rkhunter --update
[13:52:02] Info: Environment shell is /bin/bash; rkhunter is using dash
[13:52:02] Info: Using configuration file '/etc/rkhunter.conf'
[13:52:02] Info: Installation directory is '/usr'
[13:52:02] Info: Using language 'en'
[13:52:02] Info: Using '/var/lib/rkhunter/db' as the database directory
[13:52:02] Info: Using '/usr/share/rkhunter/scripts' as the support script directory
[13:52:02] Info: Using '/usr/local/sbin /usr/local/bin /usr/sbin /usr/bin /sbin /bin /usr/libexec /usr/local/libexec' as the command directories
[13:52:02] Info: Using '/var/lib/rkhunter/tmp' as the temporary directory
[13:52:02] Info: X will be automatically detected
[13:52:02] Info: Found the 'basename' command: /usr/bin/basename
[13:52:02] Info: Found the 'diff' command: /usr/bin/diff
[13:52:02] Info: Found the 'dirname' command: /usr/bin/dirname
[13:52:02] Info: Found the 'file' command: /usr/bin/file
[13:52:02] Info: Found the 'find' command: /usr/bin/find
[13:52:02] Info: Found the 'ifconfig' command: /usr/sbin/ifconfig
[13:52:02] Info: Found the 'ip' command: /usr/sbin/ip
[13:52:02] Info: Found the 'ipcs' command: /usr/bin/ipcs
[13:52:02] Info: Found the 'ldd' command: /usr/bin/ldd
[13:52:02] Info: Found the 'lsattr' command: /usr/bin/lsattr
[13:52:02] Info: Found the 'lsmod' command: /usr/sbin/lsmod
[13:52:02] Info: Found the 'lsof' command: /usr/bin/lsof
[13:52:02] Info: Found the 'mktemp' command: /usr/bin/mktemp
[13:52:02] Info: Found the 'netstat' command: /usr/bin/netstat
[13:52:02] Info: Found the 'numfmt' command: /usr/bin/numfmt
[13:52:02] Info: Found the 'perl' command: /usr/bin/perl
[13:52:02] Info: Found the 'pgrep' command: /usr/bin/pgrep
[13:52:02] Info: Found the 'ps' command: /usr/bin/ps
[13:52:02] Info: Found the 'pwd' command: /usr/bin/pwd
[13:52:02] Info: Found the 'readlink' command: /usr/bin/readlink
[13:52:02] Info: Found the 'stat' command: /usr/bin/stat
[13:52:03] Info: Found the 'strings' command: /usr/bin/strings
[13:52:03] Info: Found the 'curl' command: /usr/bin/curl
[13:52:03] Info: The mirrors file will be rotated
[13:52:03] Info: Only local mirrors will be used
[13:52:03] Info: The mirrors file will not be updated
[13:52:03] Info: Logging to log file: /var/log/rkhunter.log
[13:52:03] Info: Locking is not being used
[13:52:03]
[13:52:03] Checking rkhunter data files...
[13:52:03] Info: Created temporary file '/var/lib/rkhunter/tmp/rkhunter.upd.AZry8xl8qM'
[13:52:03] Checking file mirrors.dat [ Skipped ]
[13:52:03] Info: The mirrors file has no required mirrors in it: /var/lib/rkhunter/db/mirrors.dat
[13:52:03] Warning: Download of 'programs_bad.dat' failed: Unable to determine the latest version number.
[13:52:03] Checking file programs_bad.dat [ Update failed ]
[13:52:03] Info: The mirrors file has no required mirrors in it: /var/lib/rkhunter/db/mirrors.dat
[13:52:03] Warning: Download of 'backdoorports.dat' failed: Unable to determine the latest version number.
[13:52:03] Checking file backdoorports.dat [ Update failed ]
[13:52:03] Info: The mirrors file has no required mirrors in it: /var/lib/rkhunter/db/mirrors.dat
[13:52:03] Warning: Download of 'suspscan.dat' failed: Unable to determine the latest version number.
[13:52:03] Checking file suspscan.dat [ Update failed ]
[13:52:03] Info: The mirrors file has no required mirrors in it: /var/lib/rkhunter/db/mirrors.dat
[13:52:03] Checking file i18n versions [ Update failed ]
[13:52:03] Warning: Download of 'i18n.ver' failed: Unable to determine the latest version number.
[13:52:03]
[13:52:03] Info: End date is Пт 22 сен 2023 13:52:03 EEST
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 23 сен 2023, 01:39
Olej писал(а): ↑22 сен 2023, 13:34
tiger
Код: Выделить всё
olej@R420:~$ aptitude search tiger
p libwiredtiger-dev - high performance, scalable, NoSQL, extensible platform (development)
p libwiredtiger-java - Java language support for WiredTiger
p libwiredtiger0 - high performance, scalable, NoSQL, extensible platform (library)
p tiger - security auditing and intrusion detection tools for Linux
p tiger-otheros - security auditing and intrusion detection scripts for Unix based systems
p tigervnc-common - Virtual network computing; Common software needed by servers
p tigervnc-scraping-server - Virtual network computing server performing X screen scraping
p tigervnc-standalone-server - Standalone virtual network computing server
p tigervnc-tools - Virtual network computing; Tools for both clients and servers
p tigervnc-viewer - Virtual network computing client for X
p tigervnc-xorg-extension - Virtual network computing X server extension
p wiredtiger - high performance, scalable, NoSQL, extensible platform for data management
Код: Выделить всё
olej@R420:~$ sudo apt install tiger
[sudo] пароль для olej:
Чтение списков пакетов… Готово
Построение дерева зависимостей… Готово
Чтение информации о состоянии… Готово
Будут установлены следующие дополнительные пакеты:
chkrootkit john john-data tripwire
Предлагаемые пакеты:
lynis
Следующие НОВЫЕ пакеты будут установлены:
chkrootkit john john-data tiger tripwire
Обновлено 0 пакетов, установлено 5 новых пакетов, для удаления отмечено 0 пакетов, и 0 пакетов не обновлено.
Необходимо скачать 7.676 kB архивов.
После данной операции объём занятого дискового пространства возрастёт на 28,7 MB.
Хотите продолжить? [Д/н] y
Пол:1 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 tripwire amd64 2.4.3.7-4 [1.849 kB]
Пол:2 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 chkrootkit amd64 0.55-4 [352 kB]
Пол:3 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 john-data all 1.8.0-4ubuntu3 [4.561 kB]
Пол:4 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/main amd64 john amd64 1.8.0-4ubuntu3 [212 kB]
Пол:5 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 tiger amd64 1:3.2.4~rc1-3 [702 kB]
Получено 7.676 kB за 3с (2.926 kB/s)
Предварительная настройка пакетов …
Выбор ранее не выбранного пакета tripwire.
(Чтение базы данных … на данный момент установлено 572748 файлов и каталогов.)
Подготовка к распаковке …/tripwire_2.4.3.7-4_amd64.deb …
Распаковывается tripwire (2.4.3.7-4) …
Выбор ранее не выбранного пакета chkrootkit.
Подготовка к распаковке …/chkrootkit_0.55-4_amd64.deb …
Распаковывается chkrootkit (0.55-4) …
Выбор ранее не выбранного пакета john-data.
Подготовка к распаковке …/john-data_1.8.0-4ubuntu3_all.deb …
Распаковывается john-data (1.8.0-4ubuntu3) …
Выбор ранее не выбранного пакета john.
Подготовка к распаковке …/john_1.8.0-4ubuntu3_amd64.deb …
Распаковывается john (1.8.0-4ubuntu3) …
Выбор ранее не выбранного пакета tiger.
Подготовка к распаковке …/tiger_1%3a3.2.4~rc1-3_amd64.deb …
Распаковывается tiger (1:3.2.4~rc1-3) …
Настраивается пакет tripwire (2.4.3.7-4) …
Generating site key (this may take several minutes)...
Generating local key (this may take several minutes)...
Настраивается пакет john-data (1.8.0-4ubuntu3) …
Настраивается пакет chkrootkit (0.55-4) …
Настраивается пакет tiger (1:3.2.4~rc1-3) …
Creating config file /etc/tiger/tigerrc with new version
Настраивается пакет john (1.8.0-4ubuntu3) …
Обрабатываются триггеры для mailcap (3.70+nmu1ubuntu1) …
Обрабатываются триггеры для desktop-file-utils (0.26+mint3+victoria) …
Обрабатываются триггеры для gnome-menus (3.36.0-1ubuntu3) …
Обрабатываются триггеры для man-db (2.10.2-1) …
Во время установки, в ncurses, будет задавать множество вопросов:
-
Вложения
-
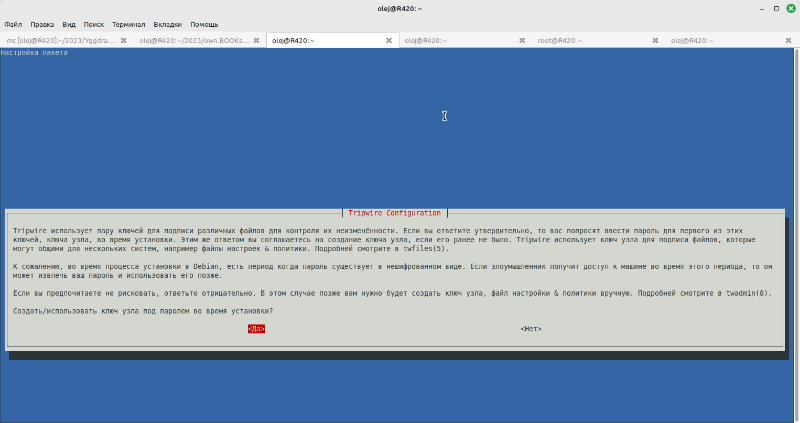
- Снимок экрана от 2023-09-23 01-35-52.png (76.04 КБ) 914 просмотров
-
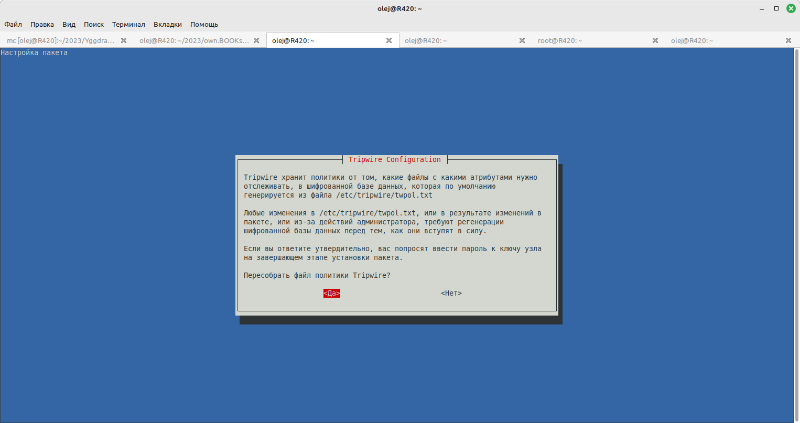
- Снимок экрана от 2023-09-23 01-36-54.png (55.13 КБ) 914 просмотров
-
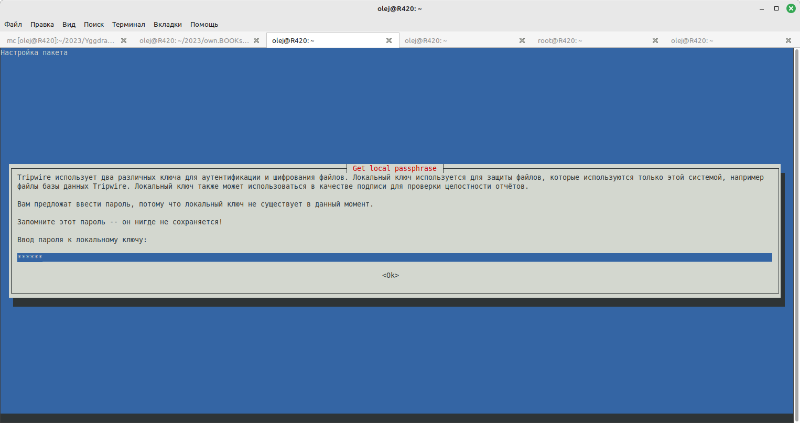
- Снимок экрана от 2023-09-23 01-37-47.png (51.69 КБ) 914 просмотров
-
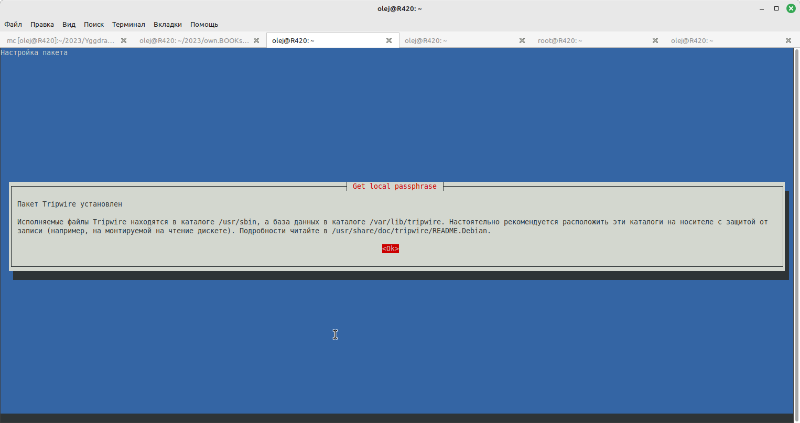
- Снимок экрана от 2023-09-23 01-38-21.png (42.21 КБ) 914 просмотров
Olej
-
Olej
- Писатель
- Сообщения: 21338
- Зарегистрирован: 24 сен 2011, 14:22
- Откуда: Харьков
-
Контактная информация:
Непрочитанное сообщение
Olej » 23 сен 2023, 01:48
Olej писал(а): ↑22 сен 2023, 13:34
lynis
Код: Выделить всё
olej@R420:~$ aptitude search lynis
p lynis - Инструмент аудита безопасности для систем, основанных на Unix
Код: Выделить всё
olej@R420:~$ sudo apt install lynis
[sudo] пароль для olej:
Чтение списков пакетов… Готово
Построение дерева зависимостей… Готово
Чтение информации о состоянии… Готово
Будут установлены следующие дополнительные пакеты:
menu
Предлагаемые пакеты:
apt-listbugs debsecan debsums samhain aide fail2ban menu-l10n gksu | kde-runtime | ktsuss
Следующие НОВЫЕ пакеты будут установлены:
lynis menu
Обновлено 0 пакетов, установлено 2 новых пакетов, для удаления отмечено 0 пакетов, и 0 пакетов не обновлено.
Необходимо скачать 581 kB архивов.
После данной операции объём занятого дискового пространства возрастёт на 3.164 kB.
Хотите продолжить? [Д/н] y
Пол:1 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 lynis all 3.0.7-1 [227 kB]
Пол:2 http://ubuntu.mirrors.omnilance.com/ubuntu jammy/universe amd64 menu amd64 2.1.47ubuntu4 [354 kB]
Получено 581 kB за 1с (407 kB/s)
Выбор ранее не выбранного пакета lynis.
(Чтение базы данных … на данный момент установлено 573225 файлов и каталогов.)
Подготовка к распаковке …/archives/lynis_3.0.7-1_all.deb …
Распаковывается lynis (3.0.7-1) …
Выбор ранее не выбранного пакета menu.
Подготовка к распаковке …/menu_2.1.47ubuntu4_amd64.deb …
Распаковывается menu (2.1.47ubuntu4) …
Настраивается пакет lynis (3.0.7-1) …
Created symlink /etc/systemd/system/timers.target.wants/lynis.timer → /lib/systemd/system/lynis.timer.
lynis.service is a disabled or a static unit not running, not starting it.
Настраивается пакет menu (2.1.47ubuntu4) …
Обрабатываются триггеры для desktop-file-utils (0.26+mint3+victoria) …
Обрабатываются триггеры для doc-base (0.11.1) …
Обработка 1 добавленный файл doc-base...
Обрабатываются триггеры для gnome-menus (3.36.0-1ubuntu3) …
Обрабатываются триггеры для man-db (2.10.2-1) …
Обрабатываются триггеры для install-info (6.8-4build1) …
Обрабатываются триггеры для mailcap (3.70+nmu1ubuntu1) …
Обрабатываются триггеры для menu (2.1.47ubuntu4) …
Olej
Сейчас этот форум просматривают: нет зарегистрированных пользователей и 0 гостей